MyBook Users Urged to Unplug Devices from Internet – Krebs on Security
[ad_1]
Laborious drive big Western Digital is urging customers of its MyBook Reside model of community storage drives to disconnect them from the Web, warning that malicious hackers are remotely wiping the drives utilizing a vital flaw that may be triggered by anybody who is aware of the Web deal with of an affected gadget.
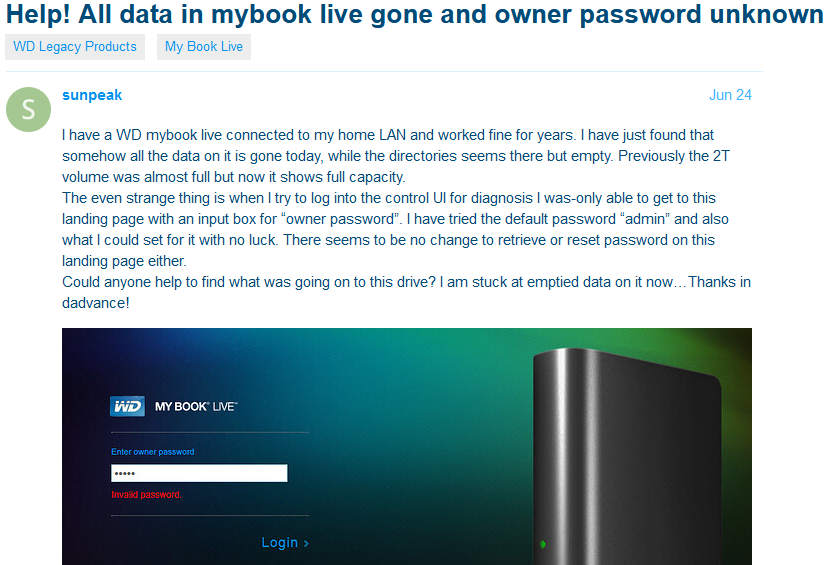
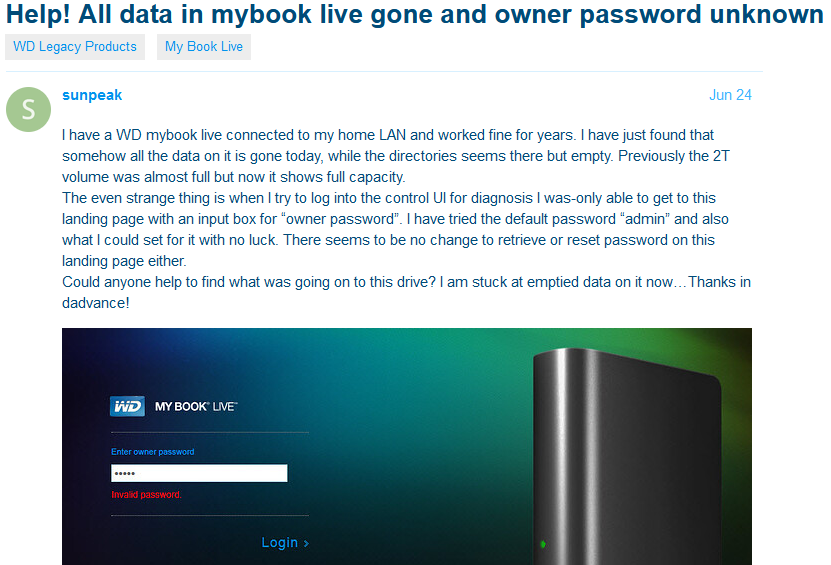
One in every of many related complaints on Western Digital’s person discussion board.
Earlier this week, Bleeping Laptop and Ars Technica pointed to a heated dialogue thread on Western Digital’s person discussion board the place many shoppers complained of discovering their MyBook Reside and MyBook Reside Duo gadgets utterly wiped of their information.
“Western Digital has decided that some My E book Reside and My E book Reside Duo gadgets are being compromised by means of exploitation of a distant command execution vulnerability,” the corporate stated in a press release June 24. “In some circumstances, this compromise has led to a manufacturing unit reset that seems to erase all information on the gadget. The My E book Reside and My E book Reside Duo gadgets obtained its last firmware replace in 2015. We perceive that our prospects’ information is essential. We’re actively investigating the problem and can present an up to date advisory when we have now extra info.”
Western Digital’s temporary advisory features a hyperlink to an entry within the Nationwide Vulnerability Database for CVE-2018-18472. The NVD writeup says Western Digital WD My E book Reside and WD My E book Reside Duo (all variations) have a root Distant Command Execution bug.
“It may be triggered by anybody who is aware of the IP deal with of the affected gadget, as exploited within the wild in June 2021 for manufacturing unit reset instructions,” NVD wrote.
Study the CVE hooked up to this flaw and also you’ll discover it was issued in 2018. The NVD’s advisory credit VPN reviewer Wizcase.com with reporting the bug to Western Digital three years in the past, again in June 2018.
In some methods, it’s outstanding that it took this lengthy for susceptible MyBook gadgets to be attacked: The 2018 Wizcase writeup on the flaw consists of proof-of-concept code that lets anybody run instructions on the gadgets because the omnipotent “root” person.
Western Digital’s response on the time was that the affected gadgets had been now not supported and that prospects ought to keep away from connecting them to the Web. That response additionally prompt this bug has been current in its gadgets for at the very least a decade.
“The vulnerability report CVE-2018-18472 impacts My E book Reside gadgets initially launched to the market between 2010 and 2012,” reads a reply from Western Digital that Wizcase posted to its weblog. “These merchandise have been discontinued since 2014 and are now not coated underneath our gadget software program assist lifecycle. We encourage customers who want to proceed working these legacy merchandise to configure their firewall to forestall distant entry to those gadgets, and to take measures to make sure that solely trusted gadgets on the native community have entry to the gadget.”
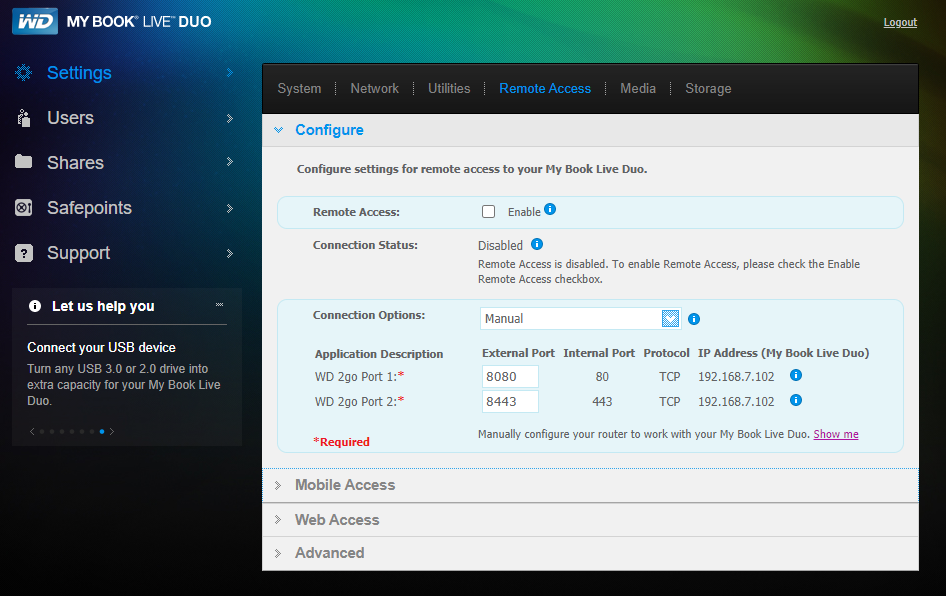
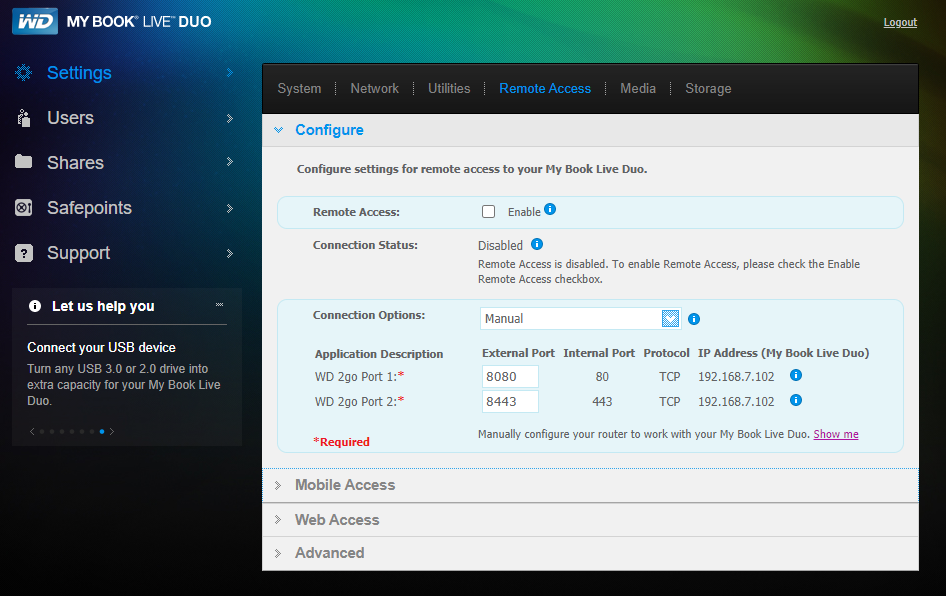
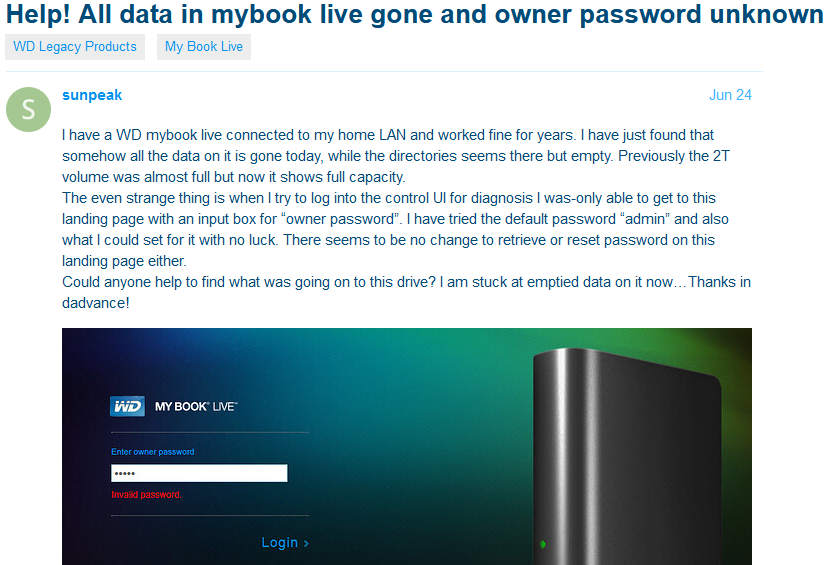
An area administration web page for the MyBook Reside Duo.
Wizcase stated the flaw it present in MyBook gadgets additionally could also be current in sure fashions of WD MyCloud community hooked up storage (NAS) gadgets, though Western Digital’s advisory makes no point out of its MyCloud line being affected.
The susceptible MyBook gadgets are widespread amongst residence customers and small companies as a result of they’re comparatively feature-rich and cheap, and could be upgraded with further storage fairly simply. However these merchandise additionally make it easy for customers to entry their information remotely over the Web utilizing a cell app.
I’m guessing it’s primarily customers who’ve configured their MyBooks to be remotely accessible who’re experiencing these unlucky drive wipes. Regardless, it’s most likely most secure to look at Western Digital’s recommendation and disconnect any MyBooks you might have from ethernet entry.
In case you’d nonetheless prefer to hold your MyBook linked to your native community (at the very least till yow will discover an acceptable backup in your backups), please make double certain distant entry will not be enabled in your gadget settings (see screenshot above).
[ad_2]
Source link